For years, businesses protected their data like a medieval castle: build a thick wall (a…
Read More
Over half of UK businesses make critical mistakes with cloud security, often misjudging how much protection their providers actually offer. Rapid growth in cyberattacks means companies in Lancashire and Manchester face serious risks if gaps go unchecked. Strong cloud security is not just a technical detail. It shapes your daily business safety, client trust, and legal standing. Understanding key threats and protective strategies can help you stay one step ahead.
Key Takeaways
| Point | Details |
|---|---|
| Understanding Shared Responsibility | Cloud security involves a shared responsibility between providers and businesses; companies must secure their data and access controls. |
| Recognizing Threats | Phishing, AI-powered threats, and ransomware attacks highlight the critical need for proactive cybersecurity measures. |
| Implementing Technologies | Utilising technologies like Multi-Factor Authentication and encryption tools is essential for protecting cloud assets. |
| Prioritizing Compliance | Compliance with regulations like Cyber Essentials and GDPR is necessary for lawful cloud operations and data protection. |
Table of Contents
- Defining Cloud Security And Core Concepts
- Types Of Cloud Security Threats
- Essential Cloud Security Technologies And Tools
- Compliance And Regulatory Requirements In The UK
- Best Practices For Cloud Security Management
Defining Cloud Security and Core Concepts
Cloud security is more complex than most Lancashire and Manchester businesses realise. It’s not just about storing data online—it’s about protecting your digital assets in an increasingly interconnected environment.
According to Data Buzz Ltd, many UK businesses fundamentally misunderstand the shared responsibility model in cloud security. Most assume their cloud provider handles all security aspects, when in reality, the responsibility is split:
- Cloud providers secure the underlying infrastructure
- Businesses must secure their specific data, access controls, and compliance
Research from Gradeon highlights that cloud security complexity is driving its importance for businesses across Lancashire and the North West. The increasing risks of misconfiguration and the shortage of specialist talent make securing hybrid and multi-cloud environments particularly challenging.
At its core, cloud security involves protecting data, applications, and infrastructure associated with cloud computing. This means implementing robust strategies to prevent unauthorized access, data breaches, and ensure regulatory compliance—critical considerations for businesses in Preston, Blackburn, and beyond.
Types of Cloud Security Threats
For businesses across Lancashire and Manchester, understanding cloud security threats is no longer optional—it’s a critical survival strategy. These digital dangers can strike quickly, causing significant operational and financial damage.
According to SIIT Research, phishing and social engineering remain the most prevalent cloud-related threats for UK businesses. These sophisticated attacks are becoming increasingly dangerous, particularly with AI technology enhancing their deceptiveness:
- Credential theft targeting employee accounts
- Malware installation through convincing email techniques
- Unauthorized access exploiting human vulnerabilities
Prestige Cyber Guard highlights an emerging trend of AI-powered threats, including deepfake impersonations that can trick even experienced professionals. These attacks are especially dangerous for SMEs in Preston, Blackburn, and across the North West, who often lack extensive cybersecurity resources.
Beyond traditional phishing, businesses must also guard against data breaches, ransomware attacks, and insider threats. Each presents unique challenges requiring comprehensive security strategies that combine technological solutions with robust employee training and awareness programmes.
Essential Cloud Security Technologies and Tools
For businesses across Lancashire and Manchester, navigating cloud security requires a robust toolkit of technologies designed to protect digital assets and mitigate emerging cyber risks. Cloud security technologies are no longer optional—they’re fundamental to maintaining operational integrity and protecting sensitive information.
Key cloud security technologies every business should consider include:
- Multi-Factor Authentication (MFA): Adds critical layers of verification beyond simple passwords
- Encryption Tools: Protect data both in transit and at rest
- Cloud Access Security Brokers (CASB): Monitor and manage cloud application security
- Security Information and Event Management (SIEM) Systems: Provide real-time analysis of security alerts
Network segmentation and zero trust architecture represent advanced strategies for businesses in Preston, Blackburn, and across the North West. These approaches assume no inherent trust in any network connection, requiring continuous verification for every access request.
Read more about preventing cloud breaches by implementing these cutting-edge technologies. Remember, cloud security is not a one-time setup but an ongoing process of monitoring, updating, and adapting to the evolving digital threat landscape.
Here’s a summary of key cloud security technologies and their primary functions:
| Technology | Purpose | Example Benefit |
|---|---|---|
| Multi-Factor Authentication (MFA) | Extra verification for user logins | Reduces unauthorised access |
| Encryption Tools | Protects data in transit and at rest | Secures sensitive information |
| CASB | Monitors and manages cloud use | Detects risky behaviour |
| SIEM Systems | Analyses security alerts in real time | Enables rapid threat response |
| Network Segmentation | Separates critical IT resources | Limits breach impact |
| Zero Trust Architecture | Requires verification for all access | Prevents lateral attacks |
Compliance and Regulatory Requirements in the UK
For businesses across Lancashire and Manchester, cloud security compliance is not just a best practice—it’s a legal necessity. Navigating the complex landscape of regulatory requirements demands careful attention and strategic planning.
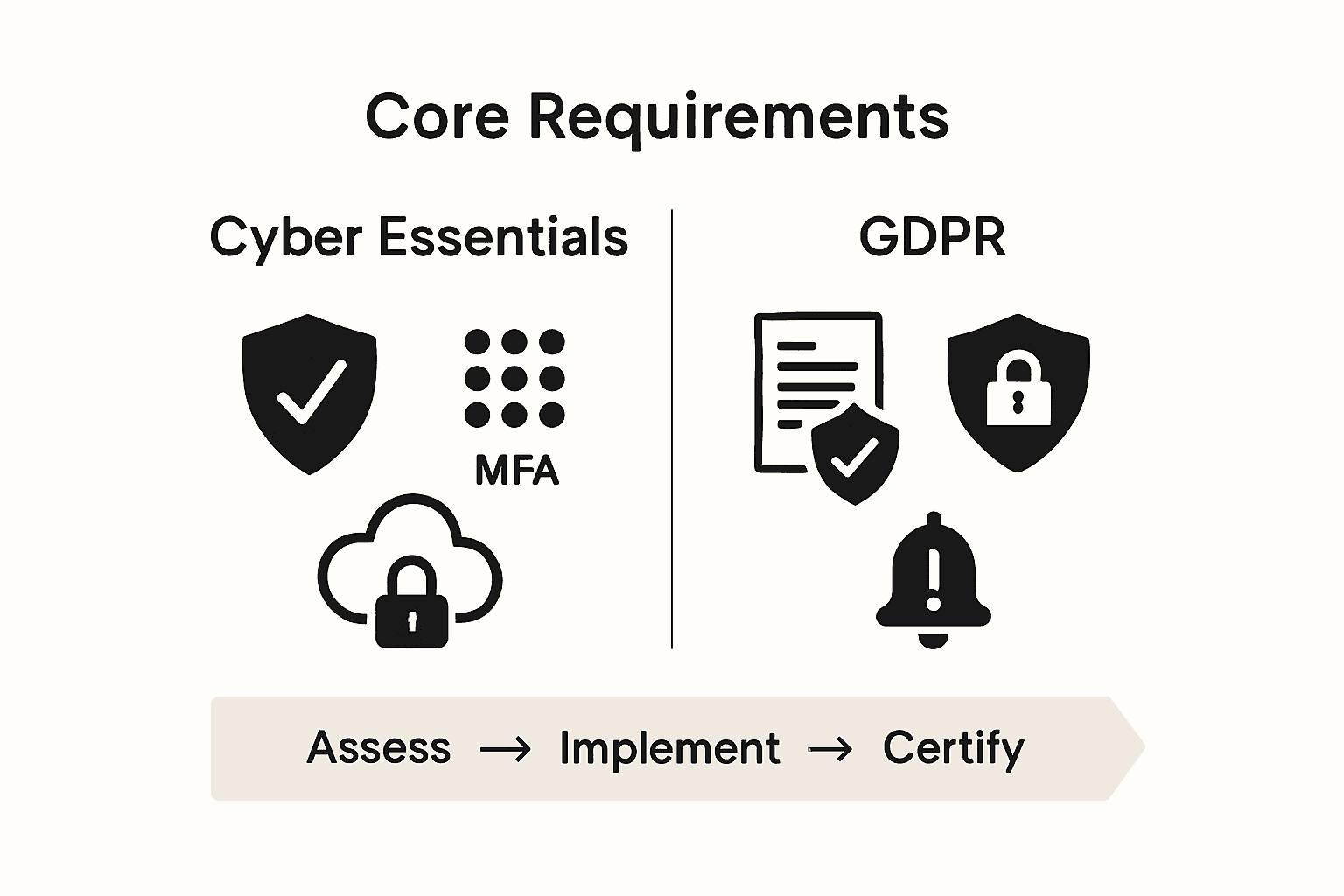
According to Wikipedia’s Cyber Essentials documentation, the UK government has established clear guidelines through the Cyber Essentials certification scheme. Since January 2022, this scheme has significantly expanded its scope to comprehensively cover cloud services:
- Mandates multi-factor authentication
- Requires stringent password and PIN controls
- Defines minimum cyber protection standards
- Applies to all cloud service implementations
Businesses in Preston, Blackburn, and across the North West must also consider additional regulatory frameworks like GDPR, which impose strict data protection requirements. This means implementing robust mechanisms for:
- Data encryption
- Access control
- Regular security audits
- Breach notification protocols
Learn more about preventing cloud breaches to ensure your cloud strategy remains compliant and secure. Compliance is an ongoing journey, not a destination—staying informed and proactive is key to protecting your digital assets.
Best Practices for Cloud Security Management
For businesses across Lancashire and Manchester, cloud security management requires a proactive and comprehensive approach. Protecting your digital infrastructure isn’t about implementing a single solution, but creating a robust, multi-layered strategy that adapts to evolving threats.
Key best practices for effective cloud security management include:
- Regular Security Assessments: Conduct comprehensive audits of your cloud environment
- Principle of Least Privilege: Grant employees minimum access necessary for their roles
- Continuous Employee Training: Keep your team updated on latest cybersecurity threats
- Robust Backup and Recovery Plans: Ensure data can be quickly restored in case of incidents
Businesses in Preston, Blackburn, and across the North West should prioritize employee awareness as a critical component of cloud security. This means creating a culture of security consciousness where every team member understands their role in protecting sensitive information.
Explore our guide on preventing cloud breaches to develop a comprehensive security strategy. Remember, cloud security is not a one-time implementation but an ongoing process of monitoring, learning, and adapting to protect your most valuable digital assets.
Protect Your Business with Trusted Cloud Security Experts
Are you worried about misconfigurations, compliance risks or sophisticated cloud threats? If your business in Lancashire or Manchester faces uncertainty about cloud security responsibilities, you are not alone. Many UK companies struggle to keep data safe and meet regulations while lacking the in-house expertise or tools mentioned in this guide. Visit our Cloud Solutions page to see how we help local businesses secure every aspect of their cloud infrastructure and protect sensitive information.
Take real action to futureproof your business today. The risk of cyber attacks and compliance failures is growing rapidly, so do not wait for a breach before acting. Speak to our Lancashire-based specialists for tailored cloud security solutions that include managed support, advanced technology, and ongoing compliance. Make contact quickly at J700 Group or explore how we strengthen digital protection by visiting our Cyber Security resource hub. Your peace of mind starts now.
Frequently Asked Questions
What is cloud security?
Cloud security involves protecting data, applications, and infrastructure associated with cloud computing through various strategies to prevent unauthorized access, data breaches, and ensure compliance with regulations.
What are the types of cloud security threats faced by businesses?
Common cloud security threats include phishing, social engineering, data breaches, ransomware attacks, and insider threats. It’s essential to implement comprehensive security strategies to mitigate these risks.
What technologies are essential for effective cloud security management?
Key technologies include Multi-Factor Authentication (MFA), encryption tools, Cloud Access Security Brokers (CASB), Security Information and Event Management (SIEM) systems, network segmentation, and zero trust architecture.
How can businesses ensure compliance with cloud security regulations?
Businesses can ensure compliance by following guidelines such as the Cyber Essentials certification, implementing multi-factor authentication, controlling access, encrypting data, conducting regular audits, and establishing breach notification protocols.