For years, businesses protected their data like a medieval castle: build a thick wall (a…
Read More
Nearly 40% of UK businesses reported cyber attacks in the past year, yet many still leave critical systems exposed. For Lancashire and Manchester companies, a single breach can mean lost revenue and damaged trust. By taking practical, proven steps, you can build stronger defences and protect your business from costly digital threats.
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Conduct a thorough IT assessment | Identify vulnerabilities in your systems to protect against cyber threats before they are exploited by attackers. |
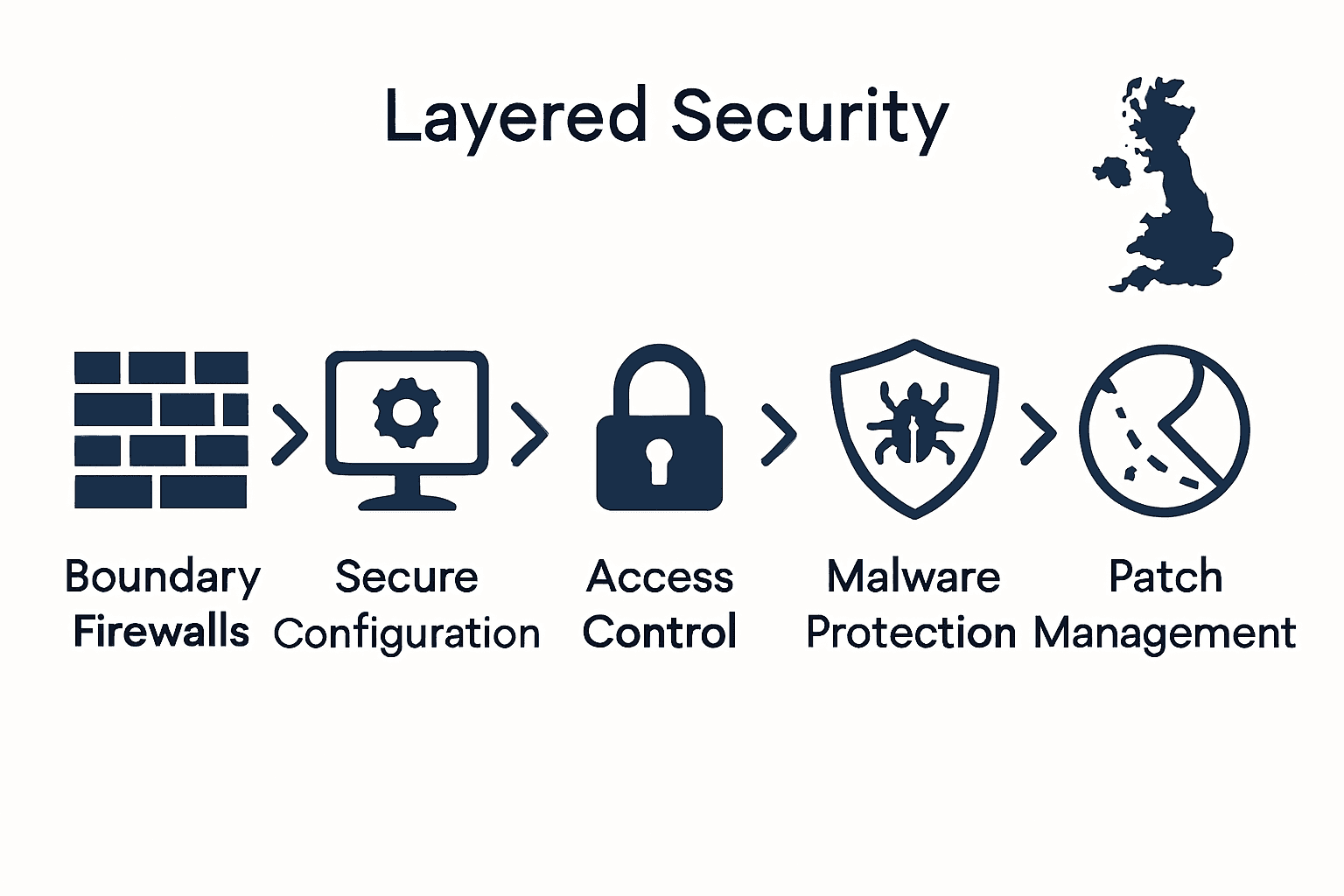
| 2. Implement five essential cybersecurity controls | Utilize boundary firewalls, secure configurations, access controls, malware protection, and patch management to significantly reduce vulnerabilities. |
| 3. Provide ongoing staff training | Regularly educate employees about cybersecurity threats and best practices to transform them into a first line of defense. |
| 4. Deploy a multi-layered backup strategy | Create multiple data backups to safeguard against data loss due to cyber incidents or accidental deletions, ensuring business continuity. |
| 5. Establish ongoing security monitoring | Continuously track and analyze system activities to detect unusual patterns or potential breaches in real-time. |
Table of Contents
- Step 1: Assess Current IT Infrastructure And Risks
- Step 2: Implement Essential Cybersecurity Controls
- Step 3: Establish Staff Cybersecurity Training
- Step 4: Deploy Regular Data Backup Solutions
- Step 5: Verify Security With Ongoing Monitoring
Step 1: Assess current IT infrastructure and risks
Understanding your current IT infrastructure is the foundation of robust cybersecurity for your Lancashire and Manchester based business. This step helps you identify vulnerabilities before cybercriminals can exploit them.
Start by conducting a comprehensive inventory of all digital assets. This means mapping out every computer, server, smartphone, tablet, and network device used in your organisation. Pay special attention to remote working equipment and personal devices that connect to your business systems.
According to the Effective Vulnerability Management for Your Technology guide, creating a detailed asset register is crucial. Document each device’s operating system, age, software versions, and current patch status.
Review your network architecture carefully. Look for potential entry points that could be vulnerable to attacks. This includes examining firewall configurations, checking wireless network security, and understanding how different systems interconnect.
Pro Tip: In the 2025 Cyber Security Breaches Survey, only 48% of small businesses have undertaken cybersecurity risk assessments. By completing this step, you are already ahead of most SMEs in protecting your digital assets.
Consider engaging an external IT security professional who can provide an objective assessment. They can help you identify blind spots and recommend specific improvements tailored to your business environment.
The next step will involve translating these insights into a actionable risk mitigation strategy that addresses the specific vulnerabilities you have discovered.
Step 2: Implement essential cybersecurity controls
Now that you understand your IT infrastructure, it is time to implement robust cybersecurity controls that protect your Lancashire and Manchester business from potential threats. This critical step will help fortify your digital defences and reduce vulnerability to cyber attacks.
The National Cyber Security Centre (NCSC) recommends focusing on five essential technical controls that can prevent around 80% of common cyber attacks.
Here’s a comparison of the five essential cybersecurity controls recommended for SMEs:
| Control | Purpose | Key Actions |
|---|---|---|
| Boundary Firewalls | Block unauthorised access | Configure filters Monitor traffic |
| Secure Configuration | Minimise attack surface | Remove extra software Change default settings |
| Access Control | Restrict system access | Limit privileges Enable multi factor authentication |
| Malware Protection | Detect and remove threats | Install antivirus Enable email/web filtering |
| Patch Management | Fix known vulnerabilities | Apply updates regularly Automate where possible |
Start by implementing boundary firewalls and secure gateways. These act as your first line of defence, monitoring and controlling network traffic. Configure these systems to block suspicious incoming and outgoing connections, creating a protective shield around your digital assets.
Next, focus on secure configuration of all devices and systems. This means removing unnecessary software, disabling default accounts, and ensuring all systems are set up with minimal necessary permissions. Avoid using default passwords and implement strong, unique credentials for each system and user.
Careful access control is paramount. Limit user privileges based on job roles and implement multi factor authentication wherever possible. This ensures that even if a password is compromised, an additional layer of verification prevents unauthorized access.
Pro Tip: 10 Biggest Cybersecurity Mistakes of Small Businesses highlights that many SMEs overlook the importance of granular access management.
Install comprehensive malware protection across all devices and ensure regular updates. This includes antivirus software, email filtering, and web protection tools that can detect and neutralize potential threats before they infiltrate your systems.
Finally, establish a robust patch management process. Regularly update all software, operating systems, and applications to address known vulnerabilities. Automated patch management can help ensure no system is left unprotected.
The next step involves creating a comprehensive incident response plan that outlines how your business will react to potential security breaches.
Step 3: Establish staff cybersecurity training
Human error remains one of the most significant vulnerabilities in any cybersecurity strategy. By establishing comprehensive staff cybersecurity training, you can transform your Lancashire and Manchester business team into a robust first line of defence against potential cyber threats.
Start by developing a structured training programme that goes beyond a one-time information session. According to the Information Commissioner’s Office (ICO), effective cybersecurity training should be ongoing, role-specific, and integrated into your organisation’s core processes.
Begin with a comprehensive induction programme for new employees. Cover fundamental principles of data protection, recognising phishing attempts, and understanding the importance of secure password management. Make these sessions interactive and engaging to ensure maximum retention.
Implement regular knowledge checks and refresher courses. How Often to Train Employees on Cybersecurity Awareness suggests conducting training at least quarterly to keep cybersecurity knowledge current and top of mind.
Tailor your training to different roles within your organisation. A marketing team member will have different cybersecurity risks compared to someone in finance or IT. Develop role-specific modules that address unique vulnerabilities and responsibilities.
Pro Tip: Use real-world examples and simulated phishing exercises to make training more practical and memorable.
Create a tracking system to monitor training completion and assess understanding. The ICO recommends using knowledge checks and maintaining records of employee training progress. This not only ensures comprehensive coverage but also demonstrates your commitment to cybersecurity if audited.
Consider bringing in external cybersecurity experts for specialised workshops. These sessions can provide fresh perspectives and up-to-date insights into emerging cyber threats specific to SMEs in the UK.
Remember that cybersecurity training is not a one-time event but an ongoing process of education, awareness, and adaptation. The next step involves developing a comprehensive incident response plan that complements your staff training efforts.
Step 4: Deploy regular data backup solutions
Protecting your business data is crucial for ensuring continuity and resilience in the face of potential cyber incidents. Deploying robust backup solutions will safeguard your Lancashire and Manchester business against data loss from cyber attacks, hardware failures, or accidental deletions.
According to the 2025 Cyber Security Breaches Survey, 83% of businesses now have cloud or alternative backup systems. This means implementing a comprehensive backup strategy is no longer optional but essential for modern SMEs.
Start by selecting a multi layered backup approach. This involves creating at least three copies of your critical data: your primary working copy, a local backup on an external hard drive or network attached storage, and a secure offsite or cloud backup.
Choose reliable cloud storage solutions that offer encryption and multiple data centre locations. Ensure these services provide automatic backup scheduling, versioning capabilities, and quick recovery options. This allows you to restore systems rapidly in case of an incident.
Implement a clear backup schedule that matches your business needs. For most SMEs, daily incremental backups with weekly full backups provide an optimal balance between data protection and system performance.
Pro Tip: Test your backup and recovery process quarterly to ensure you can actually restore data when needed.
Consider using Cyber Attacks Devastate UK Icons as a reference to understand real world implications of inadequate data protection.
Ensure your backup systems are themselves secured with strong authentication, encryption, and access controls. Treat backup infrastructure with the same security rigour you apply to your primary systems.
The next step involves developing a comprehensive disaster recovery plan that integrates these backup solutions into a broader business continuity strategy.
Step 5: Verify security with ongoing monitoring
Ongoing security monitoring transforms your cybersecurity from a static defence to a dynamic shield that adapts and responds to emerging threats. For your Lancashire and Manchester business, this means creating a proactive system that continuously assesses and protects your digital infrastructure.
The UK Government’s security policy handbook emphasises the critical importance of implementing robust logging and monitoring strategies. This goes beyond simple occasional checks. You need a comprehensive approach that tracks and analyses system activities in real time.
Start by establishing comprehensive logging across all critical systems. This means capturing detailed records of user activities, network traffic, system changes, and access attempts. Configure your logging to capture essential details without creating overwhelming volumes of data.
Invest in security information and event management (SIEM) tools that can aggregate and analyse logs from multiple sources. These sophisticated systems can help you detect unusual patterns or potential security breaches that might otherwise go unnoticed.
10 Biggest Cybersecurity Mistakes of Small Businesses highlights how many SMEs overlook the importance of continuous monitoring, leaving critical vulnerabilities undetected.
Pro Tip: Set up automated alerts for suspicious activities like multiple failed login attempts, unexpected administrative changes, or unusual data transfer volumes.
Consider partnering with a managed security service provider who can offer 24/7 monitoring and rapid incident response. For smaller businesses without dedicated IT security teams, this provides professional oversight and expertise.
Regularly review and update your monitoring strategies. Cyber threats evolve rapidly, so your monitoring approach must be equally dynamic. Conduct quarterly reviews of your logging and monitoring configurations to ensure they remain effective against current threat landscapes.
The next step involves developing a comprehensive incident response plan that builds upon the insights gained from your ongoing security monitoring efforts.
Ready to Secure Your SME with Proven Cybersecurity Solutions?
You have explored essential steps for protecting your business in the article “Cybersecurity Checklist for SMEs: Secure Your UK Business”. If you worry about unpatched systems, untrained staff, or gaps in security monitoring, you are not alone. Many SMEs in Lancashire and Manchester face the same challenges. Staying ahead of evolving cyber threats can feel overwhelming, especially when mistakes can lead to costly downtime or lost data. Our experience with managed IT and cybersecurity puts control back in your hands.
See how other local businesses benefit from robust security measures by exploring our Cyber Security Resources.
Act now to safeguard your business against risk. Let our local team design and manage your digital defences so you can focus on growth with confidence. Start a conversation today by visiting our Contact Page or discover more practical tips in our IT Tips and Tricks Archive. Secure your future with support from J700 Group.
Frequently Asked Questions
What steps should I take to assess my current IT infrastructure for cybersecurity?
To assess your current IT infrastructure, start by conducting a comprehensive inventory of all digital assets, including computers, servers, and user devices. Document each asset’s operating system, software versions, and patch status. This will help you identify vulnerabilities that need addressing.
How can I implement essential cybersecurity controls for my SME?
Begin by focusing on five key controls: boundary firewalls, secure configurations, access control, malware protection, and patch management. Make sure to apply these controls correctly to reduce vulnerabilities by up to 80%. Establish a schedule for regular monitoring and updates to these systems.
What should I include in staff cybersecurity training?
Include ongoing, interactive training that covers data protection principles, phishing recognition, and secure password management. Implement role-specific modules that focus on the unique cybersecurity risks relevant to different positions within your organization, ensuring this training occurs at least quarterly.
How should I set up regular data backups to protect my business data?
Select a multi-layered backup approach that creates at least three copies of critical data: a primary working copy, a local backup, and a secure offsite or cloud backup. Establish a regular backup schedule, ideally daily for incremental backups and weekly for full backups, to ensure maximum data protection.
What continuous monitoring strategies should I implement for effective cybersecurity?
Establish comprehensive logging across all critical systems to capture user activities, system changes, and access attempts. Invest in monitoring tools that detect unusual patterns or potential breaches, and automate alerts for activities that indicate possible security incidents.
How can I develop a comprehensive incident response plan?
Begin by documenting all procedures to follow in the event of a cybersecurity incident. Ensure the plan details roles and responsibilities, communication protocols, and mitigation strategies, aiming to create a clear roadmap that your team can follow within 24 hours of a breach.