For manufacturers, downtime isn’t just frustrating, it’s expensive. When production stops, everything slows down. Orders…
Read More
An email landed in my inbox this week from “Jonathan Cundliffe” — our Managing Director.
It was polite. Appreciative. Marked Critical Update. And it was a complete fraud.
I caught it. But in a busy office, under deadline pressure, with 47 other unread emails waiting? Most people wouldn’t.
Here’s the anatomy of the scam and what to look for before it costs your business.
The Email That Almost Looked Real
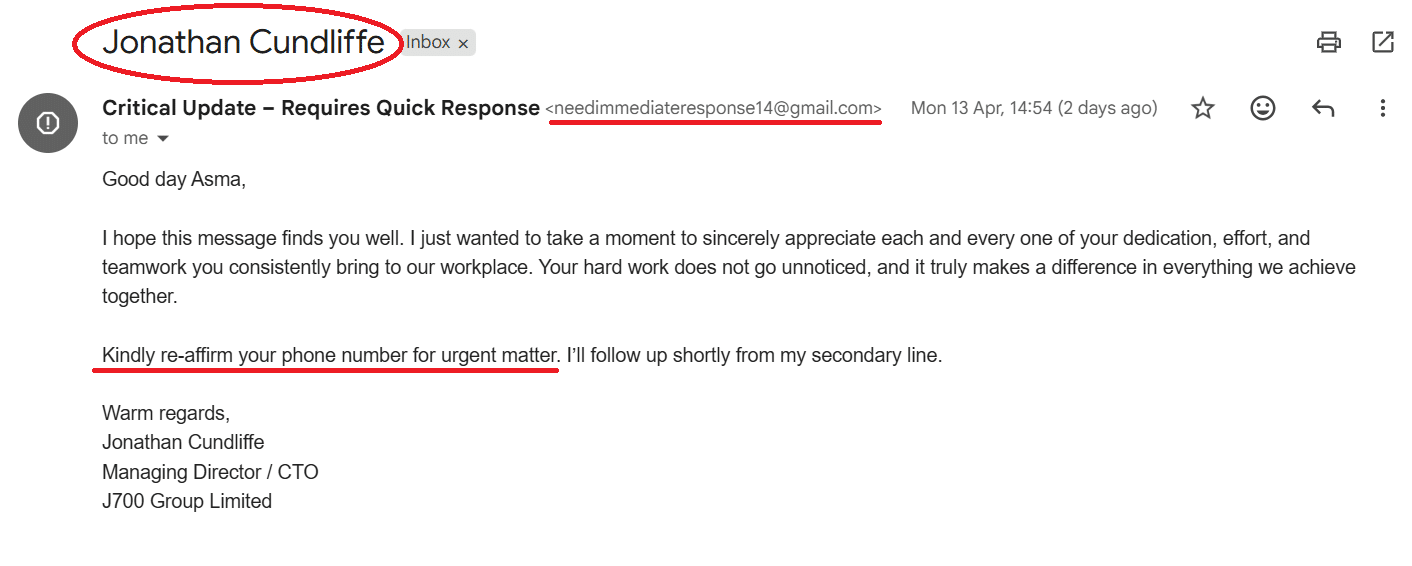
From: Jonathan Cundliffe <[email protected]>
Subject: Critical Update – Requires Quick Response
“Good day Asma, I just wanted to take a moment to sincerely appreciate each and every one of your dedication… Kindly re-affirm your phone number for urgent matter. I’ll follow up shortly from my secondary line.”
Looks fine at a glance, right? Here’s why it isn’t.
🚩 The sender address is the first giveaway
The name says Jonathan Cundliffe. The actual address is a random Gmail account.
No director at any professional organisation sends company business from Gmail. This is called display name spoofing, scammers count on you reading the name and never checking the address. Always check the address.
🚩 Flattery is deliberate
That gushing first paragraph isn’t warmth, it’s a technique. Compliments trigger a subconscious desire to reciprocate. You feel appreciated, so you want to help quickly. That’s exactly what the scammer needs.
🚩 Phone number request is step one of two
This isn’t the actual scam, it’s the setup. Once they have your number, they move to WhatsApp or SMS, posing as the director stuck in a meeting, asking for a fast bank transfer or gift card “just this once.” It’s a two-stage trap, and stage one looks completely harmless.
🚩 The language feels slightly off
“Kindly re-affirm.” It’s polite, but is it Jonathan? Impersonators can mimic tone, but they can rarely replicate the specific way your boss actually writes. If the wording feels even slightly unfamiliar, that instinct is worth trusting.
What Is CEO Fraud?
CEO fraud is a type of cyber attack where a criminal impersonates a senior executive, a Managing Director, CEO, or CFO, to trick an employee into handing over money or sensitive information.
It doesn’t rely on viruses or malicious links. There’s nothing to click, nothing to scan. It’s pure manipulation. The attacker bets on one thing: that you trust your boss and won’t stop to question them.
The scam usually arrives as an urgent email. It might ask you to confirm your phone number, process a quick bank transfer, or share payroll details, always with a reason why it needs to happen now, and often with a reason why you shouldn’t mention it to anyone else.
It’s also far more common than most businesses realise. The FBI estimates that CEO fraud has cost businesses worldwide over £19 billion in losses. And unlike a data breach, there’s rarely a way to get the money back once it’s gone.
What I Did Next (And What You Should Do Too)
I didn’t reply and I didn’t click anything. I contacted Jonathan directly, by phone, not by email and confirmed in 30 seconds it was a scam.
That’s it. One extra step would have saved a potential bank transfer, a data breach, or worse.
At J700 Group, we call this out-of-band verification: when something feels urgent and involves money or personal data, you confirm it through a completely separate channel. Always.
The Honest Truth About Cyber Security
Your firewall won’t catch this. Your spam filter probably won’t either, this email made it straight to my inbox.
The only thing that caught it was training, habit, and a workplace culture where questioning a suspicious “director’s” email isn’t seen as being difficult, it’s seen as doing your job.
Has your team been trained to spot this specific type of attack?
We work with businesses across Lancashire and Manchester to build that culture, the tools, the training and the processes that catch scams before they land. If you want to know how protected your team actually is, call us on 0333 7721 700 or get in touch today.
Recommended:
Artificial Intelligence is no longer something businesses are experimenting with. In 2026, it’s becoming part…
Read MoreAn email landed in my inbox this week from “Jonathan Cundliffe” — our Managing Director.…
Read MoreFor years, businesses protected their data like a medieval castle: build a thick wall (a…
Read MoreFor many small and medium-sized businesses, cybersecurity is still viewed as an IT problem. Firewalls,…
Read MoreCloud technology is no longer a luxury or a cost-saving alternative to on-site servers. For…
Read MoreRemember when we jokingly wondered if Apple was borrowing our name? Well, the rumours were…
Read MoreAI hasn’t just changed the way we work, it has completely rewritten the rulebook for…
Read MoreFor many businesses, the office phone is like part of the furniture, it’s always there,…
Read MoreWe are thrilled to announce a significant milestone in the J700 Group journey. To keep…
Read MoreFor years, many small and medium-sized business owners in the North West have operated under…
Read MoreIn a modern healthcare setting, the stethoscope and the blood pressure cuff aren’t the only…
Read MoreWhen people hear the word cybersecurity, they often imagine complex systems, expensive software and specialist…
Read MoreAs we count down to midnight, most of us are thinking about gym memberships or…
Read MoreIt’s Christmas Eve in Lancashire. The Preston bypass is a nightmare, the last-minute dash to…
Read MoreFor many businesses, the Christmas period means quieter offices, reduced staffing and systems left running…
Read MoreOr: Why we’d like to have a word with Tim Cook this Christmas. There are…
Read MoreHackers Love Christmas: Learn Why your Business Could be at Risk This Holiday SeasonThe festive…
Read MoreIn recent months, high-profile companies like Land Rover and Co-op have made headlines due to…
Read MoreExplore 7 essential tips for effective cloud solutions comparison to find the best fit for…
Read MoreLearn how to secure business data for UK SMEs with this step-by-step guide focused on…
Read MoreCybersecurity basics explained for UK businesses—core concepts, major threats, essential safeguards, and compliance requirements. A…
Read MoreDiscover the essential role of IT support desks, core functions, key benefits, types of support,…
Read MoreDiscover 10 microsoft 365 alternatives for UK SMEs, comparing features and benefits to help your…
Read MoreDiscover the best microsoft 365 alternatives in our comparison of 10 top products to enhance…
Read MoreDiscover a business connectivity checklist with 7 actionable steps to boost IT reliability, security, and…
Read MoreDiscover 7 essential business continuity planning steps to protect your SME. Learn practical strategies for…
Read MoreSmall Business Office 365 comprehensive guide for UK SMEs: core features, setup process, security essentials,…
Read MoreSmall Business Office 365 guide for UK firms. Learn core features, setup, security, costs, and…
Read MoreSmall business Office 365 guide covering essential features, security, costs, local support, and practical benefits…
Read MoreFollow this cybersecurity checklist for SMEs to secure your business in Lancashire and Manchester. Step-by-step…
Read MoreFollow this cybersecurity checklist for SMEs to boost protection, reduce risks, and secure business data…
Read MoreCloud security explained: A comprehensive guide for UK businesses covering threat types, protection strategies, compliance,…
Read MoreData protection strategies for UK SMEs—types, key components, GDPR compliance, business risks, and best practices…
Read MoreWhy cybersecurity matters for UK businesses: core concepts, main risks, common threats, legal requirements, and…
Read MoreComprehensive guide to IT issues Lancashire businesses face, including security threats, system downtime, cloud solutions,…
Read MoreComprehensive guide on cyber security threats in the UK. Learn common types, key characteristics, real-world…
Read MoreFollow this IT security checklist for a step-by-step process to secure your business effectively in…
Read MoreExplore the benefits of managed IT services for businesses in Manchester and Lancashire, enhancing efficiency…
Read MoreExplore the role of cybersecurity in business. Understand its importance, how it works, and key…
Read More