For years, businesses protected their data like a medieval castle: build a thick wall (a…
Read More
Losing important digital files can feel like watching years of hard work vanish in seconds. Yet, here is a surprise. Professional data recovery experts can recover information even from storage devices that are physically damaged or corrupted, using advanced forensic tools that scan drives at microscopic levels. Most people assume deleted or lost data is gone forever but with the right techniques, what once seemed impossible is often just the start of a recovery story that saves vital business records and irreplaceable personal memories.
Table of Contents
- What Is Data Recovery And Why Is It Important?
- Key Concepts In The Data Recovery Process
- Types Of Data Loss And Their Impacts
- How Data Recovery Techniques Work
- Real-World Applications Of Data Recovery Solutions
Quick Summary
| Takeaway | Explanation |
|---|---|
| Data recovery is vital for businesses. | It prevents loss of critical documents and supports operational continuity. |
| Understand types of data loss. | Recognising accidental deletion, hardware failure, and software corruption is key for effective recovery strategies. |
| Utilise professional data recovery services. | Experts employ advanced techniques to retrieve lost information, especially from damaged storage devices. |
| Implement a robust backup strategy. | Regular backups and comprehensive data protection plans can significantly reduce the risk of data loss. |
| Stay updated on recovery technologies. | Be aware of evolving recovery tools and methods, especially those involving artificial intelligence and machine learning. |
What is Data Recovery and Why is it Important?
Data recovery represents a critical technological process designed to retrieve and restore digital information that has been lost, accidentally deleted, corrupted, or becomes inaccessible through various technological failures. This sophisticated procedure helps businesses and individuals protect and regain valuable digital assets when standard access methods fail.
Understanding the Core Concept
At its fundamental level, data recovery involves specialised techniques and software tools that can reconstruct digital information from storage devices like hard drives, solid state drives, USB drives, and cloud storage systems. The process goes beyond simple file restoration, addressing complex scenarios where data might seem permanently lost.
University of Cambridge emphasises the critical nature of data protection, highlighting that modern businesses rely extensively on digital information for operational continuity.
Why Data Recovery Matters
Data recovery becomes essential for several compelling reasons:
- Business Continuity: Prevents permanent loss of critical business documents, financial records, and customer information
- Legal Compliance: Helps organisations maintain regulatory requirements for data preservation
- Financial Protection: Mitigates potential financial losses associated with irretrievable digital information
Professional data recovery services employ advanced forensic techniques that can reconstruct information from physically damaged storage media, deleted partitions, or systems compromised by malware. These experts utilise specialised hardware and software algorithms capable of scanning storage devices at microscopic levels, recovering fragments of data that might otherwise be considered permanently lost.
Whether dealing with accidental deletion, hardware failure, or complex system crashes, data recovery provides a crucial lifeline for preserving digital information across personal and professional contexts.
Key Concepts in the Data Recovery Process
Data recovery represents a complex technological procedure involving multiple sophisticated techniques and strategic approaches to retrieve and restore digital information across various scenarios and storage environments.
Fundamental Recovery Mechanisms
Understanding data recovery requires recognising the intricate methods professionals employ to reconstruct digital assets. These mechanisms operate through advanced scanning technologies that can penetrate damaged storage media, identifying and reconstructing fragmented data segments that conventional access methods cannot retrieve.
UK Data Service emphasises that effective data recovery strategies are built upon comprehensive backup and restoration protocols.
Critical Recovery Strategies
Professional data recovery approaches typically encompass several strategic methodologies:
- Logical Recovery: Addressing software level data loss through file system reconstruction
- Physical Recovery: Repairing hardware damage and extracting data from compromised storage devices
- Forensic Recovery: Comprehensive data retrieval techniques used in complex investigative scenarios
These strategies require specialised knowledge of digital storage architectures, file system structures, and advanced forensic technologies.
To support reader understanding, the following table explains the main data recovery strategies mentioned in the article and when each is most appropriately applied.
| Recovery Strategy | Description | Typical Application Scenario |
|---|---|---|
| Logical Recovery | Addresses software-level data loss via file system reconstruction | Accidental deletion, software corruption |
| Physical Recovery | Repairs hardware and extracts data from compromised devices | Mechanical drive failure, physical device damage |
| Forensic Recovery | Uses investigative methods for comprehensive retrieval | Cyber attacks, legal or complex investigative cases |
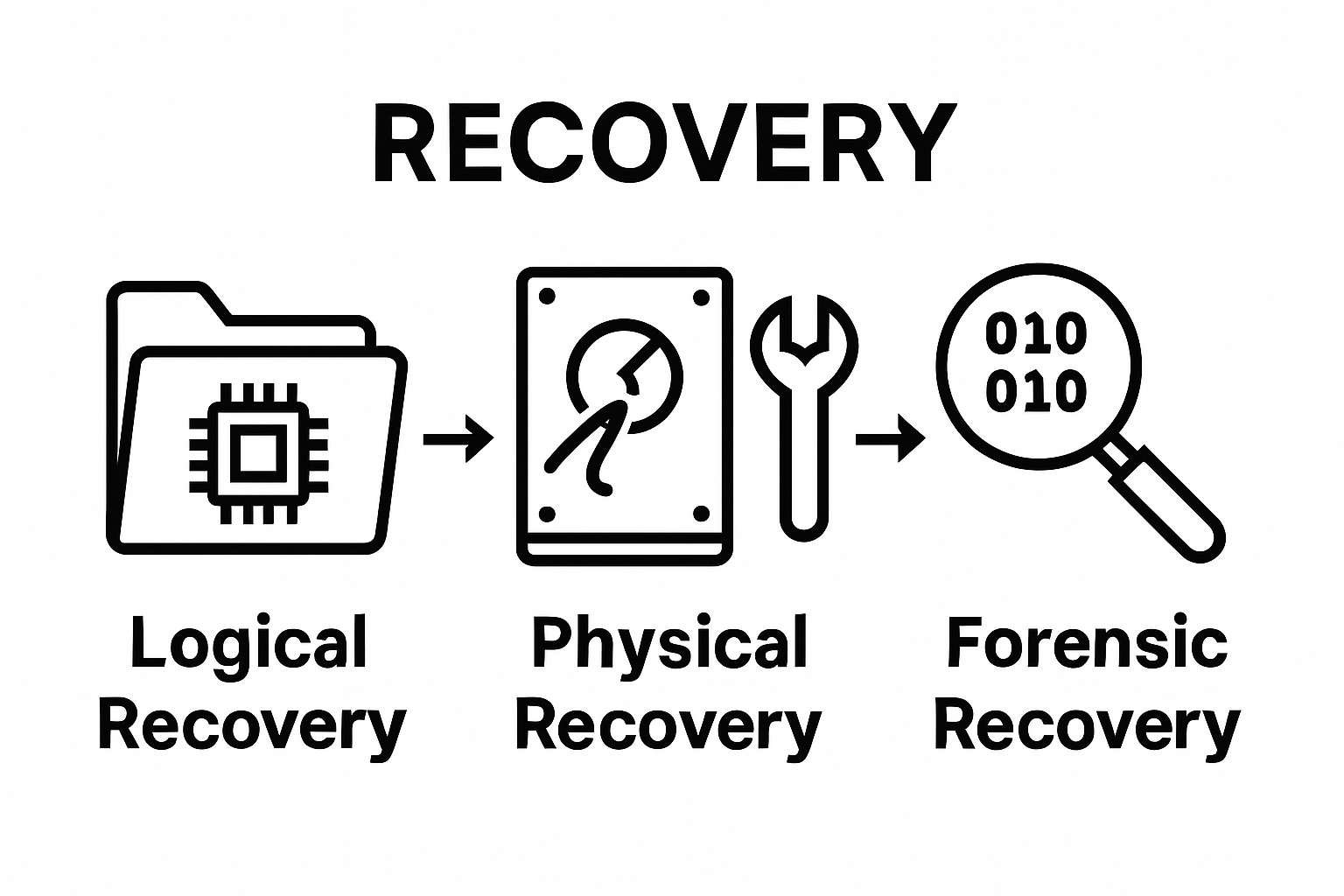
Successful data recovery depends on rapid intervention, specialised technical expertise, and a nuanced understanding of how digital information is structured and stored across different technological platforms. By employing sophisticated forensic techniques, experts can often retrieve seemingly irretrievable digital assets, providing critical support for businesses and individuals facing potential permanent data loss.
Types of Data Loss and Their Impacts
Data loss represents a complex and multifaceted challenge that can significantly disrupt business operations and personal digital ecosystems. Understanding the various mechanisms and potential consequences of data loss is crucial for developing robust prevention and recovery strategies.
Categories of Data Loss
Data loss can manifest through diverse technological and human-induced scenarios, each presenting unique challenges and potential risks. Comprehensive data protection strategies must account for these different loss mechanisms to ensure effective mitigation and recovery.
UK Government Data Quality Hub highlights the substantial economic implications of data management challenges.
Primary Data Loss Mechanisms
Organisations and individuals encounter several critical types of data loss:
- Accidental Deletion: Unintentional removal of critical files or information
- Hardware Failure: Physical deterioration of storage devices leading to data inaccessibility
- Malware and Cyber Attacks: Deliberate interference with digital information systems
- Software Corruption: Systemic failures that compromise data integrity
Each data loss mechanism carries distinct technical characteristics and potential recovery complexities.
Hardware failures might involve mechanical breakdowns in hard drives, while cyber attacks could systematically encrypt or destroy digital assets. Software corruption can emerge from system conflicts, incomplete updates, or unexpected program interactions.
The consequences of data loss extend far beyond immediate information unavailability. Businesses may experience operational disruptions, financial losses, regulatory non-compliance risks, and significant reputational damage. Personal users might face privacy breaches, loss of irreplaceable memories, or critical personal documentation.
To clarify the various forms of data loss and their respective challenges, the following table categorises each type and summarises its key impact and recovery consideration.
| Type of Data Loss | Description | Key Impact | Recovery Consideration |
|---|---|---|---|
| Accidental Deletion | Unintentional removal of files or data by human error | Loss of critical information | Often recoverable with prompt response |
| Hardware Failure | Physical deterioration or malfunction of storage devices | Data inaccessibility; potential permanent loss | May require physical device repair |
| Malware/Cyber Attacks | Malicious activity targeting digital information systems | Potential data destruction or encryption | Forensic expertise often required |
| Software Corruption | Failure of software causing compromised data integrity | Corrupted files, inaccessible information | File system reconstruction essential |
Effective data loss management requires a proactive, multifaceted approach that combines technological safeguards, regular backups, employee training, and sophisticated recovery protocols.
How Data Recovery Techniques Work
Data recovery techniques represent sophisticated technological processes designed to retrieve digital information through advanced diagnostic and reconstruction methodologies. These intricate approaches enable professionals to navigate complex scenarios of data loss and digital information restoration.
Foundational Recovery Mechanisms
Digital forensic techniques form the cornerstone of modern data recovery strategies. These methods involve comprehensive scanning and analysis of storage media at microscopic levels, identifying and reconstructing fragmented data segments that conventional access methods cannot retrieve. Professionals utilise specialised hardware and software tools capable of penetrating damaged storage environments and extracting critical information.
NHS Counter Fraud Authority highlights the nuanced approaches required for addressing various data loss scenarios.
Key Recovery Strategies
Data recovery professionals employ multiple strategic approaches depending on the specific loss scenario:
- Sector-Level Scanning: Comprehensive examination of storage device physical sectors
- File System Reconstruction: Rebuilding logical file structures and metadata
- Raw Data Extraction: Direct retrieval of binary information from compromised storage media
These techniques require deep understanding of digital storage architectures, including intricate knowledge of file system structures, hardware configurations, and potential failure mechanisms. Specialists must navigate complex challenges such as mechanical drive failures, logical file system corruption, and intentional data obfuscation.
Successful data recovery demands a combination of advanced technological tools, forensic expertise, and strategic problem-solving skills. By applying sophisticated algorithms and specialised diagnostic techniques, professionals can often retrieve seemingly irretrievable digital assets, providing critical support for businesses and individuals facing potential permanent data loss.
Real-World Applications of Data Recovery Solutions
Data recovery solutions have transcended their traditional technological boundaries, emerging as critical interventions across diverse professional and personal domains. These sophisticated techniques now play pivotal roles in preserving, protecting, and reconstructing digital information essential for organizational sustainability and individual digital asset management.
Strategic Sector Applications
Professional sectors increasingly rely on advanced data recovery methodologies to maintain operational continuity and protect critical information assets. From healthcare institutions tracking patient records to financial organizations safeguarding transactional data, these solutions provide robust mechanisms for information preservation and restoration.
UK Government AI Insights highlights the transformative potential of intelligent data management strategies.
Critical Recovery Implementation Areas
Data recovery solutions demonstrate remarkable versatility across multiple professional contexts:
- Healthcare: Reconstructing patient medical histories and critical treatment documentation
- Financial Services: Recovering transaction records and preventing potential financial discrepancies
- Legal Investigations: Retrieving digital evidence from compromised storage systems
- Research Institutions: Preserving critical research data and scientific documentation
These applications extend beyond mere technical interventions, representing crucial safeguards for institutional knowledge and individual digital assets. Professional data recovery experts deploy sophisticated forensic techniques that can reconstruct information from seemingly irretrievable sources, providing lifelines for organizations facing potential digital catastrophes.
The integration of artificial intelligence and machine learning technologies is progressively enhancing data recovery capabilities, enabling more precise, faster, and more comprehensive information restoration strategies. As digital ecosystems become increasingly complex, data recovery solutions continue to evolve, offering increasingly nuanced and powerful approaches to protecting and preserving critical digital information.
Is Your Business Data at Risk? Discover Reliable Data Recovery with J700 Group
Worried about losing important files due to accidental deletion, hardware failure or a cyber-attack? The article has shown how data loss can seriously disrupt your business, leading to downtime, financial setbacks and even damage to your reputation. Understanding the complex world of data recovery is the first step, but having a trusted local team to restore your information quickly is even more important.
At J700 Group, we specialise in advanced data recovery for Lancashire and the North West. We use the critical strategies discussed in the article, from forensic analysis to physical repair. Our expert team can help you recover files from damaged drives, corrupted systems or security incidents. Do not wait until the problem gets worse. Get in touch via our Contact Page today for a quick assessment and peace of mind. Protect your business from permanent loss and keep your operations running smoothly.
Frequently Asked Questions
What is the data recovery process?
The data recovery process involves specialised techniques and software tools designed to retrieve and restore lost, deleted, or inaccessible digital information from storage devices such as hard drives, USB drives, and cloud systems.
Why is data recovery important for businesses?
Data recovery is crucial for businesses as it helps to prevent permanent loss of essential documents, maintain legal compliance for data preservation, and mitigate potential financial losses associated with irretrievable information.
What are the types of data loss that can occur?
Data loss can occur due to various reasons such as accidental deletion, hardware failure, malware or cyber attacks, and software corruption, each requiring different recovery strategies.
How do professionals perform data recovery?
Professionals perform data recovery using advanced scanning technologies and forensic techniques to reconstruct digital information from damaged storage devices, employing methods like sector-level scanning, file system reconstruction, and raw data extraction.